Productivity
TWERT: The Ultimate Tool for Productivity and Parental Control
twert - a Free and open-source Self/Parental control program for Windows
Productivity
twert - a Free and open-source Self/Parental control program for Windows
privacy
Cybersecurity
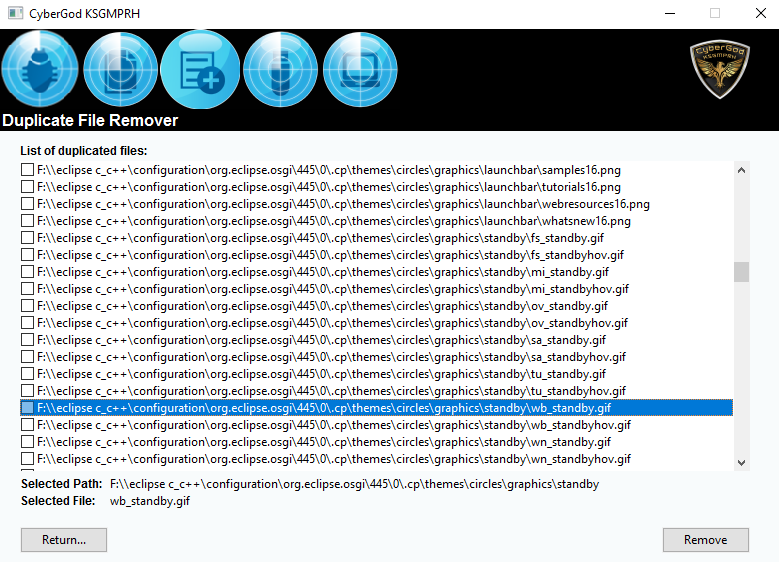
BLUESPAWN is an active defense, endpoint detection, and response tool designed for quick detection, identification, and elimination of malicious activity and malware across a network. The tool encourages user participation and contribution; suggestions for new features, bug reports, and development assistance are welcomed through their Discord server. The creation and

macos
If you have ever been concerned about the security of your MacOS device, you will be pleased to learn about macOS-Fortress. This powerful tool is a combination of firewall, blackhole, and privatizing proxy for trackers, attackers, malware, adware and spammers. It provides kernel-level, OS-level, and client-level security, making your MacOS
Cybersecurity
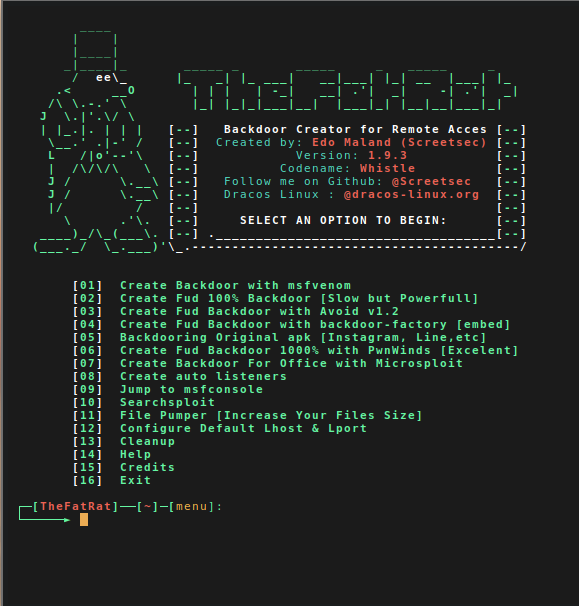
What is the FatRat? TheFatRat is an exploitation and pentesting tool designed for educational purposes. It has the capability to compile malware with popular payloads, which can then be executed on various platforms including Windows, Linux, Mac, and Android. This makes it a versatile tool for understanding the dynamics of
List
Cybersecurity
Do you know how likely it is that you’ll be hacked? Click here to find out.

Cybersecurity
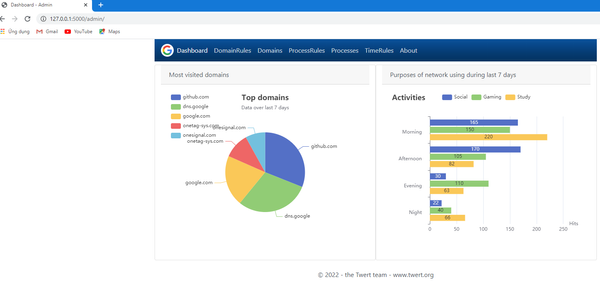
Introduction to Blocky! Blocky is an open-source local network DNS proxy and ad-blocker developed in Go. Its features include the blocking of DNS queries with external lists for ad-blocking and malware protection, as well as the allowance of whitelisting. It allows the definition of allow/denylists per client group, such
wifi
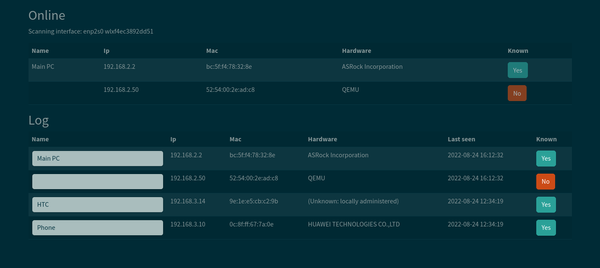
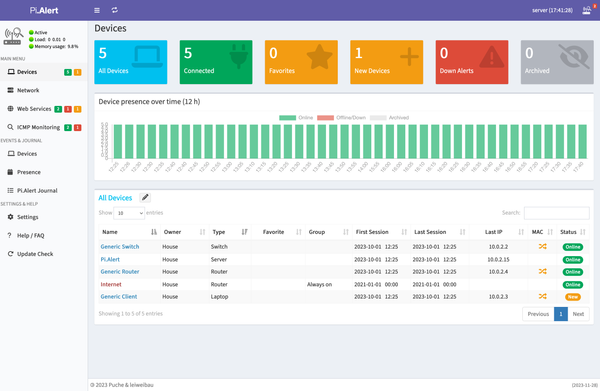
What is Pi.Alert? Pi.Alert is a comprehensive WIFI and LAN intruder detector equipped with web service monitoring for enhanced security and efficiency. This powerful tool conducts regular scans on all the devices that are connected to your WIFI or LAN. It meticulously records the identities of all known
healthcare
Digitalization is ongoing since many decades in a lot of healthcare institutions. The more digitized a healthcare institution is, the more services and quality it can be provided to patients. This, however, means that medical data and transactions which once were offline, are now possibly accessible from anywhere on Earth.
List
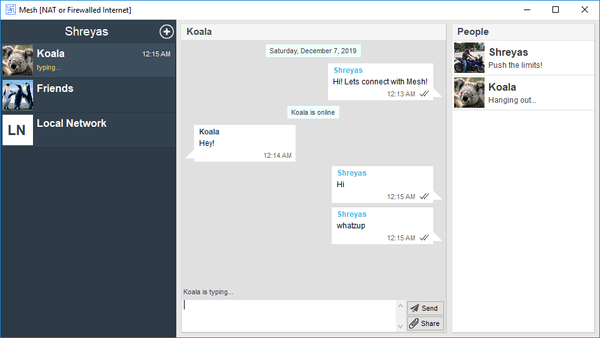
Anonymous chat apps are applications that allow users to communicate with others without revealing their identity. They offer users the ability to engage in real-time conversations while maintaining their privacy. Use-cases of Anonymous chat apps These applications are used in various scenarios. For instance, they can be used for online

Cybersecurity
In a major cybersecurity incident, an alleged database containing personal information of 85 million Egyptian citizens is reportedly up for sale on a hacking forum. The threat actor claims the database includes sensitive data such as National Identification numbers, full names, family information, mother's names, insurance numbers, and

Cybersecurity
In the dynamic world of web application security, SQL injection continues to be a dominant threat. Fear not, an abundance of open-source SQL injection tools stands ready to counter this menace. Equipped with diverse functionalities, these tools are designed to pinpoint and attack vulnerabilities, guaranteeing the unassailable strength of your

Vulnerability Scanner
A web application vulnerability scanner is an expertly crafted software program, engineered to methodically scan web applications for security vulnerabilities. It operates with precision, simulating attacks and meticulously observing the application's response to pinpoint potential weak points with absolute certainty. The scanner isn't just helpful, it&

Cybersecurity
RapidScan is a free and open-source multi-tool web app vulnerability scanner, that allows pentesters, web developers and ethical hackers looks for bugs, and security issues in any web app. It is written using Python and can be installed on any system either from source using Python or using Docker. Features