13 Top Cyber Threats Live Maps
What are Cyber threats?
A cyber threat is any event with the potential to harm any information system, disclose or leak private information, or denial a service for its intended users.
Types of cyber threats?
- DoS attacks: "Denial of Service"
- DDoS attacks: Distributed denial of service
- Malware
- Spamming and phishing
- Corporate account takeover (CATO)
- Ransomware
- Automated Teller Machine (ATM) Cash Out.
- SQL injection
- Man in the Middle (MITM) attack
- Password attacks
Cyber threats happen all the time, all over the world. It is even hard to keep track of them in real-time. Therefore, here we present to you many interactive cyber threat maps that will help you visualize the current global cyberattacks.
Here is our list of the best cyber threat real-time maps:
1- Checkpoint Threat and cyberattacks Map
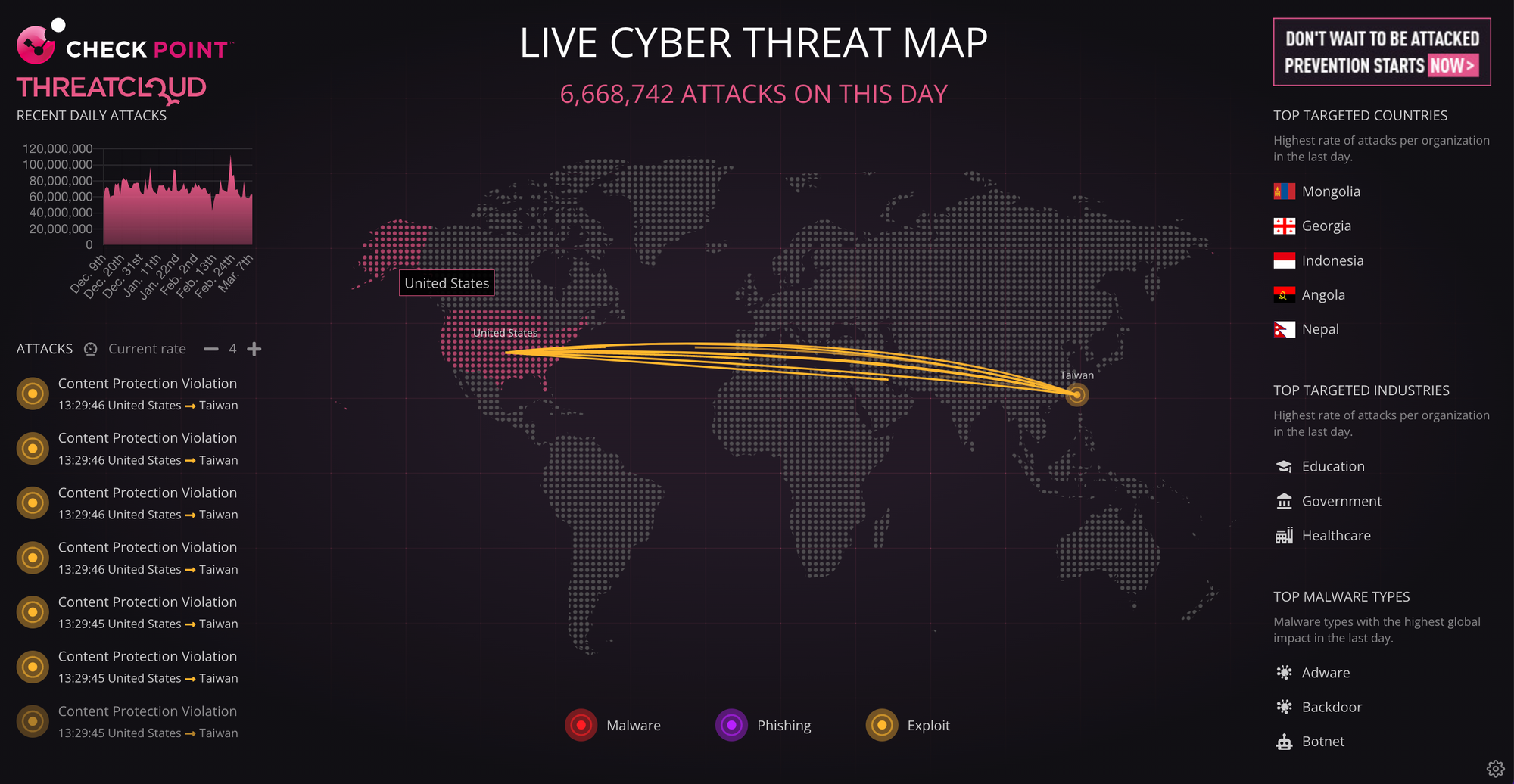
Checkpoint offers animated cyberattacks live map. With this map, you can follow the current attacks, target and source countries, and types of targeted organizations.
2- DDoS Digital Attack Map
The Digital Attack Map provides a clear view of the current DDoS attack worldwide. The user can filter attacks by type, country (source, and target), duration, and size.
This map offers a horizontal timeline visualization, table view, and embedded code that users can embed in any web page or application.
3- FireEye Cyber Threat Map
FireEye Cyber Threat Map is a minimal real-time threat visualization that gives quick insights into the current global attacks. It requires a large screen size.
4- Fortiguard Cyberattack map

Fortiguard offers a simple, fast, dynamic real-time cyberattack tracker with an interactive event visualizer.
It does not come with filtering or the options to pause the fast scrolling events, however, you can click on the attack to be redirected to its details.
5- Radware Live Threat Map
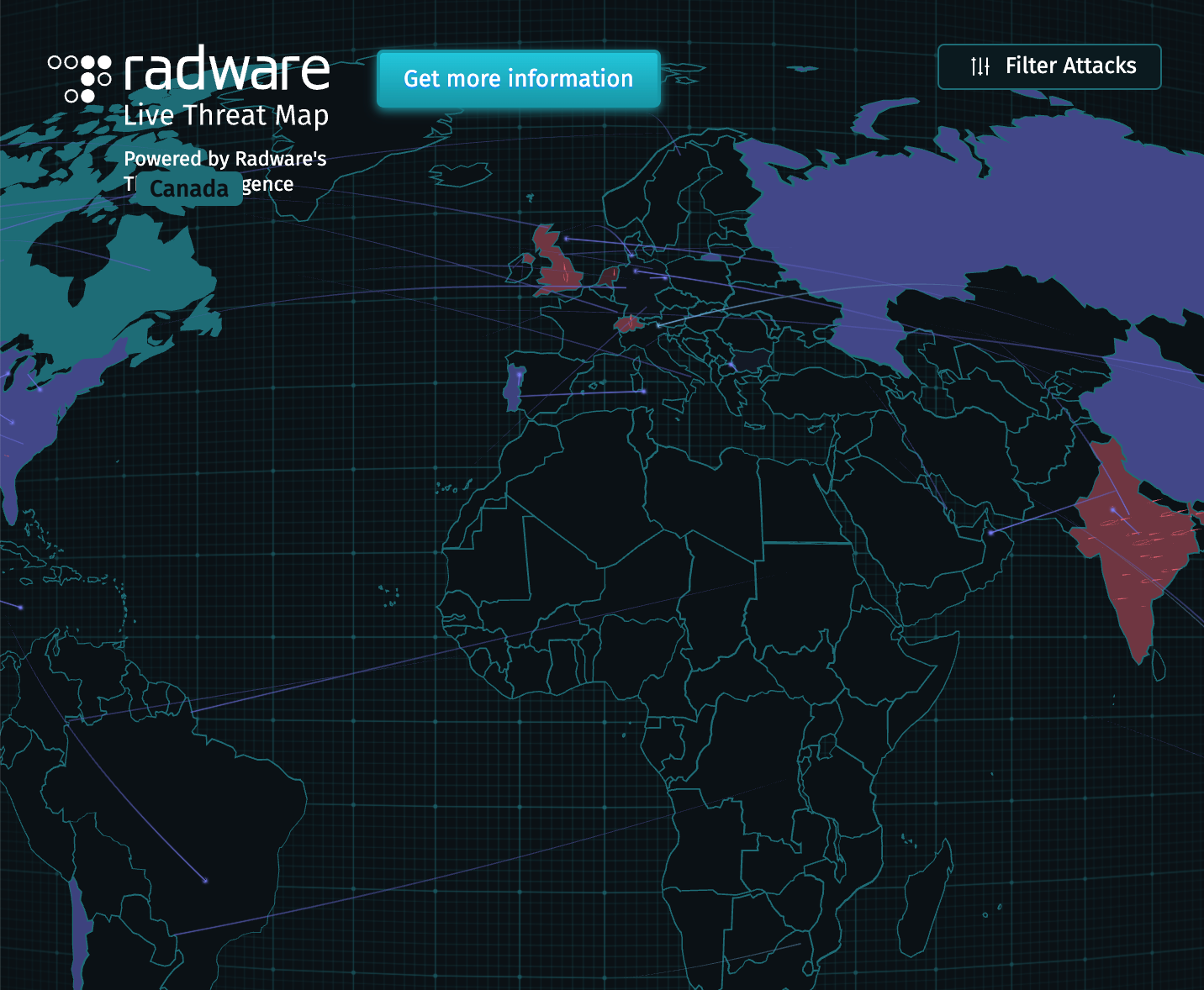
Radware offers a rich map and timeline visualization tool for cyberattacks momentarily. It also comes with several options to filter the attack events, view the events for the past hour(s), review the top attackers and the top targets, and more.
6- Bitdefender Threat Map
Bitdefender is a popular antivirus solution. Its Cyber Threats Map offers useful insights about attack locations, live attacks, and the type of attacks.
Unlike some other similar pages, Bitdefender cyber attack map is extremely lightweight and does not eat your browser resources.
7- HTTCS Cyberattacks Map
HTTCS offers their useful version of the cyberattacks map, in which the user can filter the threat and attack events
8- Threatbutt Internet Hacking Attack Attribution Map
This map is a simple retro-style map that offers a clear description of most of the current attacks, however, for some other attacks you need to register, upgrade your account to view more details.
9- Raven: The Open-source Cyberthreat map
Raven is a free, open-source project that allows anyone to self-host their cyber threat trackers and map.
The project is still in active development, but it gains the attention of many developers, and security experts all around the world.
Raven comes with a responsive map design, a lightweight and highly customizable codebase, and covers 247 counties with ~100,000 cities.
Raven is tested and proven to work fine on Google Chrome, Mozilla Firefox, and Safari browsers.
10- Live BOTNET THREATS Tracker
If you are interested to follow and viewing the current Botnet threats, then this map should be your choice.
It displays an interactive map, that visualizes real-time events provided by the Spamhaus project, the number of active bots in the last 24 hours, top worst Botnet countries, as well as top worst botnet ISPs.
11- Kaspersky real-time cyber threats map
Kaspersky offers an outstanding animated visualization threat's 3D globe map, which comes with more fancy 3D visualization.
You can also visualize the numbers of certain attack types in the last hour. By clicking on a country you can visualize the current attacks on this country.
12- Orange Real-time threats map
This map helps you to isolate and filter the attacks by their risk. It also comes with dark themes and a scrollable timeline at the footer.
13- Imperva Cyber Threat Map
Imperva offers several cyber threats and attacks trackers which include cyberattacks interactive map.
The threats are presented by different colors and circle sizes which gives an insight into the risk size. Users also can view the top attacks today, and several important details about them as requests, clients, industry, and countries (source, and target).
As our post comes to an end, we encourage you to have a look at these projects and give us your opinion about which one do you think is the best.
If you know of any other similar projects, let us know in the comments.