A Guide To Implementing Healthcare Data Security
Data security is securing data from corruption, illicit access, or theft across its lifecycle. It entails the physical, administrative and logical protection of data. It also includes organizational procedures and policies to protect against unauthorized access or use.
In the healthcare field, protecting data is a challenging task. Providers must find an equilibrium between securing patients’ data and privacy while offering quality care and complying with the extensive laws.
However, it is crucial to be knowledgeable about healthcare data security and how best to implement it. This will protect your organization from legal fines as well as financial and reputational damage.
Luckily, there are various steps for this matter. For instance, you can visit Information Technology (IT) support sites, such as Netsurit.com, if you want to outsource the task of protecting your healthcare institution and patient’s data.
Furthermore, you can read this guide if you want to know how to implement healthcare data security and other supporting information.

What Is Considered Healthcare Data?
At times called clinical or medical data, healthcare data is any information associated with any health issue, causes of death, reproductive outcomes, and life quality from any patient. Its data sources can involve claims data, surveys, disease registries, administrative and medical history, and more.
What Are The Top Cyber Threats To Healthcare Data?
A healthcare provider should know the top threats against healthcare data. Understanding these threats is one of the first steps to preventing cyber criminals from exploiting these data.
Below are some examples of cyber threats against the present healthcare industry.
- Phishing: These are social engineering attacks mainly deployed via email, although cybercriminals can also do them through text messages. In this attack, malicious actors will try to lure the potential victim into revealing their credentials, downloading malware, or sending other sensitive data that can become an entry point to a healthcare system. This is the most common access point to start any attack.
- Ransomware: This cyber-attack restricts users’ access through malicious software that infects a computer. For many years, ransomware variants have been examined and are noted to extort money from victims by presenting an on-screen alert.
- Distributed Denial Of Service (DDoS) Attacks: These online threats aim to flood the healthcare network with malicious traffic that causes it to go offline. This is also usually done to extort money without the risk associated with data exfiltration.
Eventually, you can partner with the best IT company in Grand Rapids or other areas if you want to prevent these attacks from occurring. These teams of IT experts know the best steps for this matter and will ensure quality cybersecurity service.

What Are Two Examples Of Laws Enacted To Protect Healthcare Data?
Lawmakers have implemented various regulations to ensure that healthcare institutions will protect the data they handle. Following these regulations is crucial to avoid legal fines and lawsuits.
Below are two examples of laws that you should adhere to protect healthcare data:
- The Health Information Technology for Economic and Clinical Health Act (HITECH)
HITECH was legally applied in 2009 to tackle the suggested increase in using electronic versions of Protected Health Information (PHI), otherwise known as ePHI. This law applies to all healthcare organizations with an Electronic Health Record system.
It stated that users will:
- Have access to their ePHI (Electronic Personal Health Information)
- Designate their ePHI to a third-party recipient
- Provide consent to use and share their ePHI except under three prohibitions—for the use of treatment, payment, or healthcare operations.
HITECH also encouraged more healthcare institutions to adopt electronic health records (EHRs). It also expounded upon details related to Health Insurance Portability And Accountability Act (HIPAA) to address potential flaws and laid out stricter penalties for HIPAA violations to promote adherence to security and privacy rules.
- The Health Insurance Portability And Accountability Act (HIPAA):
This is a United States law that resulted in the formulation of standards that required patients to have knowledge or consent before someone would disclose their confidential health data.
The Department of Health and Human Services (HHS) promulgated its Privacy Rule to fulfill such law’s requirements. Likewise, to safeguard the data group that the Privacy Rule covers, HHS has put HIPAA’S security Rule in place.
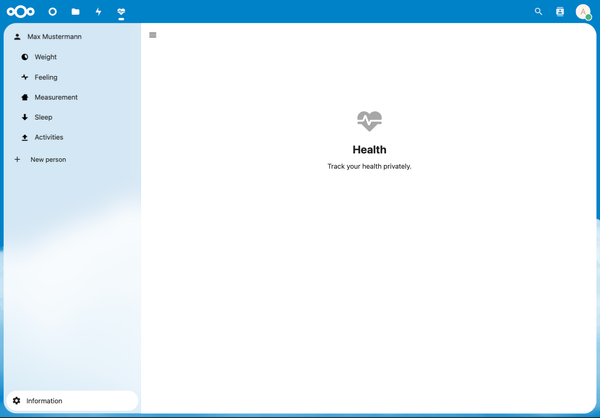
It helps to adopt HIPAA-compliant software that’s already encrypted from the start. For example, most case management software for healthcare is already equipped with the tools to protect patient data from being leaked. Just make sure you update the software regularly to prevent hacks.
What Are The Ways To Implementing Healthcare Data Security?
1- Encrypt Data
Encryption is one of the ways to secure data as it leaves or enters a healthcare institution. This security practice makes files useless whenever a cybercriminal gains access to the work device. For one, it masks these files into unreadable text.
One of the most significant issues faced by healthcare IT providers is encryption. The HIPAA law necessitated organizations to encrypt patients’ electronic health information, whether in transit or at rest. It’s crucial to follow this practice, as failure to do so can lead to fines from the HHS. More so, it can lead to a loss of patients’ trust.
2- Patch Electronic Medical Devices
There’s a chance that malicious actors will hack your monitoring tools, pacemakers, and other electronic medical devices. Thus, it would help if you patched these devices’ software to ensure they’re updated to prevent issues
3- Train Your Staff On Data Security
Your healthcare organization can more readily secure its data by providing suitable staff training regarding common cyberattacks, such as ransomware and social engineering attacks. You can also educate them on preventing actions that can lead to breaches, such as forgetting to log out of systems.
Ultimately, you can conduct regular training to enable the retention of information regarding healthcare data security. This helps them to become more ready to protect these data in their daily jobs.
Considering the increasing sophistication of cyber threats, there are more advanced measures that you must consider as well. An example is implementing a zero-trust model in your cybersecurity framework. This approach believes that trust should not be automatically given, even within your organization; every access request should be verified. In light of the Network and Information Security Directive 2 (NIS2), this move is of paramount importance. Learn more about implementing zero-trust with NIS2 compliance, which can significantly enhance your organization's cybersecurity.
4- Backup Sensitive Data
One way to protect data is to perform regular backups. This prepares your healthcare organization against any disaster, such as data breaches. You can educate your staff on data backup methods stated in your policies to start.
Final Thoughts
Your healthcare organization must implement data security to mitigate the threats that cybercriminals might deploy. This is ideal to avoid financial, legal, and reputational damage.
Consider the factors discussed above to protect your healthcare data. Some of those factors can include present regulations, top cyber threats against healthcare institutions, and steps to implement data security.
Jamie M. Hatfield
Jamie M. Hatfield is an IT student focused on cybersecurity. He creates online courses and articles to impart knowledge on securing data and IT infrastructures. When time permits, he plays golf or basketball with his relatives or friends.