KeePass: The Open-source Password Manager that sets the standards
What is KeePass?
KeePass is considered the most popular open-source password manager, and not just among end-users, but also among developers who ported it to all known platforms.
KeePass helps users to manage their passwords securely and privately, without having to worry about many technical details.
It supports several encryption standards, AES and Twofish. It also encrypts the entire database.
KeePass has dozens of ports to macOS, Linux, Windows, iOS, Android, and BlackBerry.
Because of its modular structure and plugin framework, KeePass has dozens of extensions which are built by its community over the years.
KeePass features
- Totally free and open-source
- It supports AES encryption (Advanced Encryption Standards) out-of-the-box
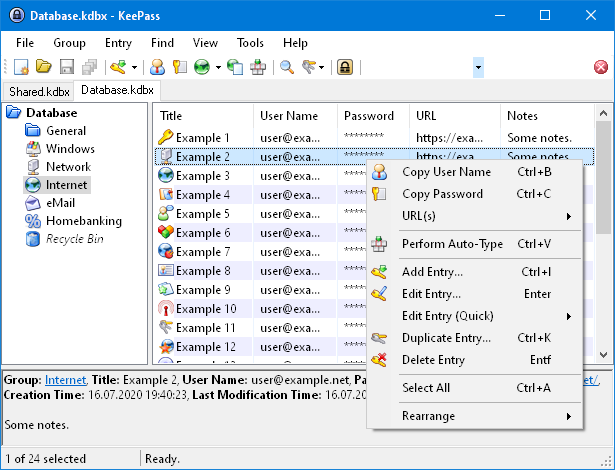
- Auto-type and drag and drop
- It encrypts anything, text fields, passwords, notes
- SHA-256 is used to hash the master key components. SHA-256 is a 256-bit cryptographically
- Offers process memory encryption
- It supports multiple user keys
- Clipboard reset option
- Backup and restore options
- Exports to various file formats: TXT, XML, HTML, and CSV files.
- Import from many file formats
- Multilingual support with more than 45 languages
- Multiple User Keys
- KeePass can work in a portable mode on Windows systems
- HTML export with a fancy design
- Strong random password generator option
- Password groups support
- Includes a powerful password generator
- A strong and handy search functionality that searches the entire database
- The master key dialog can be shown on a secure desktop, on which almost no keylogger works. Auto-Type can be protected against keyloggers, too.
- Time fields and entry attachments support
- Easy database transfer and backup
- URL field
- XML replace option
- Placeholder manager
- Database repair tool
- TAN (Only-once password) support with advanced TAN wizard
License
KeePass is distributed under the terms of the GNU General Public License version 2 or later.