Top 10 Open-source Security testing frameworks
If you're just starting off in IT security, you may be wondering, where do you even begin with the process of securing an organization's data.
There are frameworks available that can provide you with some of this information. One of the challenges with this is that every organization is going to be just a little different.
For example, your organization may have unique requirements for security based on the line of work you happen to be in. There may be compliance and regulations that you have to follow, and internally, there will be an entirely different set of security policies and tools than you might see at a different organization.
There are many security frameworks that you can use to help guide you down this particular path.
These frameworks can help you understand the different security processes available, and they can help you understand what you need to do to follow those particular processes.
Top 10 Open-Source Security check frameworks:
1- Snyk
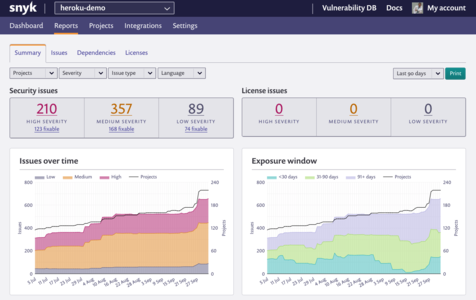
Snyk is an open-source security platform that automatically detects vulnerabilities and accelerates fixing throughout your development process. With it, you can secure all the components of the modern cloud-native application in a single platform.
It features a real-time semantic code analysis, continuous AI learning, it also embeds cloud-native application security in every development team.
Snyk is licensed under the Apache license.
GitHub: https://github.com/snyk/
2- w3af
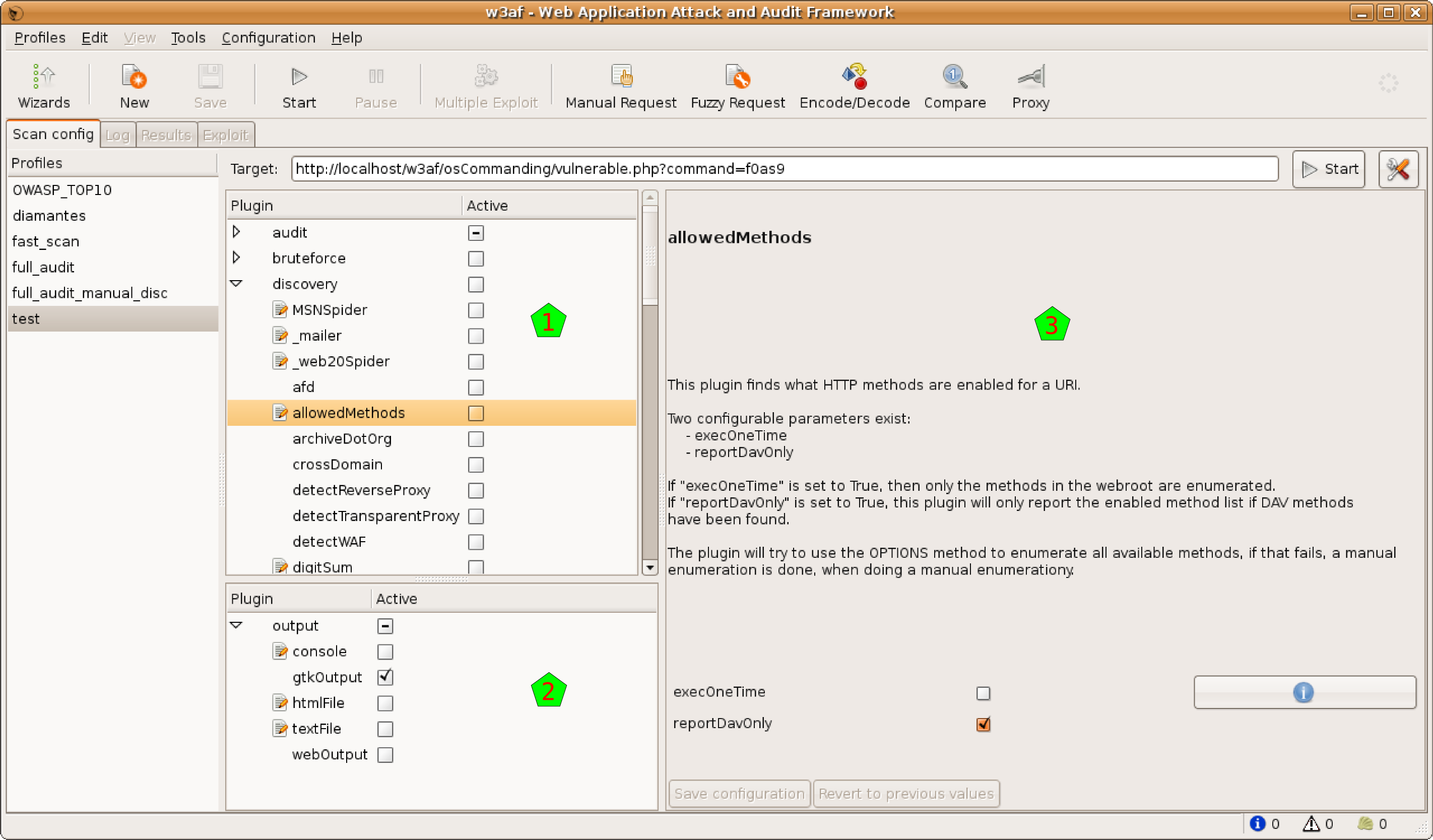
The w3af is an attack and audit framework. It is a free web application security scanner to create a framework to help you secure your web applications by finding and exploiting all web application vulnerabilities.
It helps developers and penetration testers identify and exploit vulnerabilities in their web applications.
The w3af framework was built using Python to be easy to use and licensed under GPLv2.0.
GitHub: https://github.com/andresriancho/w3af
3- Arachni
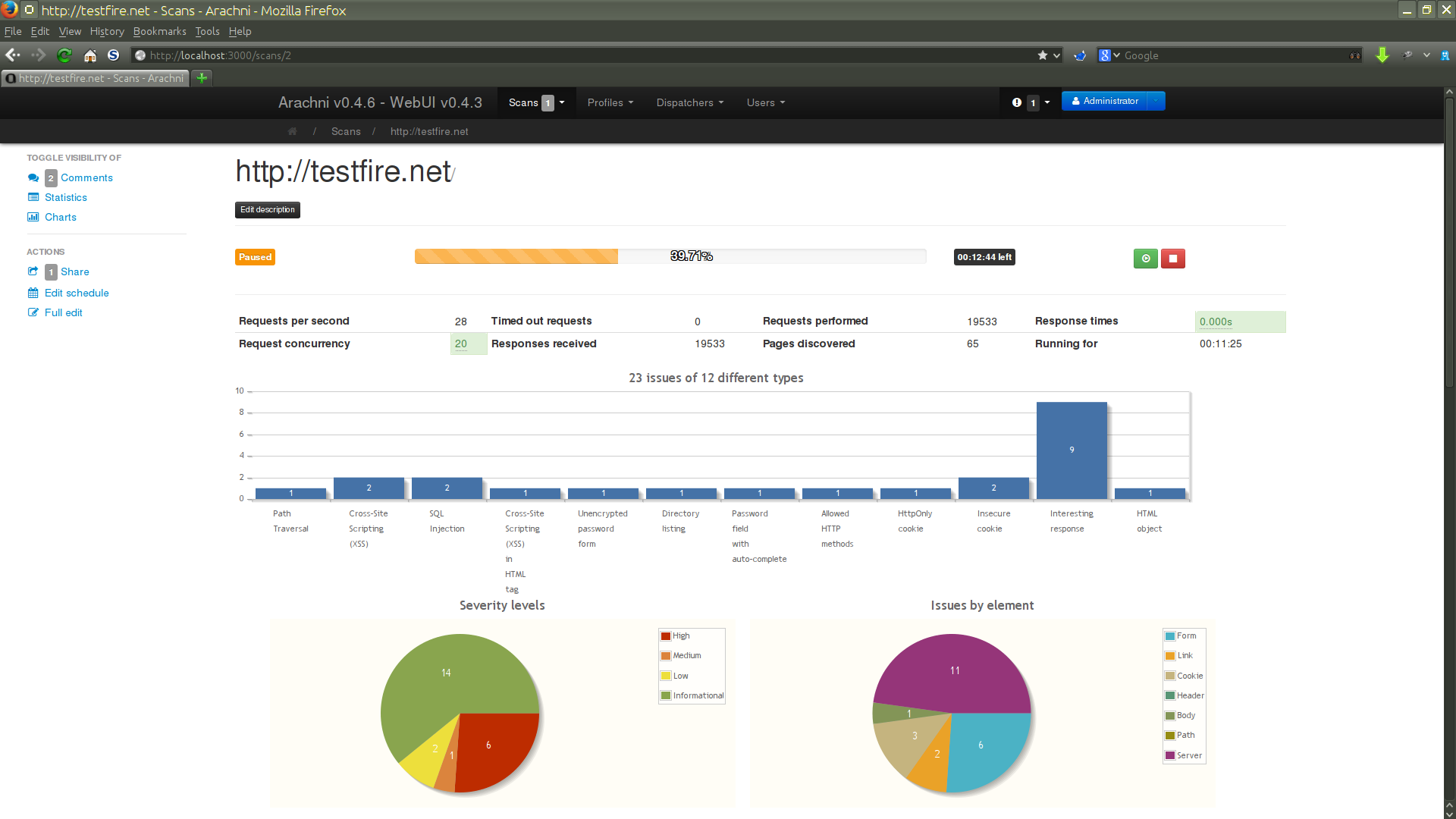
Arachni is a free and open-source Ruby framework. This is a complete web application security scanner framework that focuses on helping penetration testers and administrators evaluate the security of modern web applications.
It is multi-platform, supporting all major operating systems (MS Windows, Mac OS X, and Linux).
It is licensed under the GPL-2.0 license and written in the Ruby language.
GitHub: http://phoenix.yizimg.com/sempervictus/arachni
4- OWASP
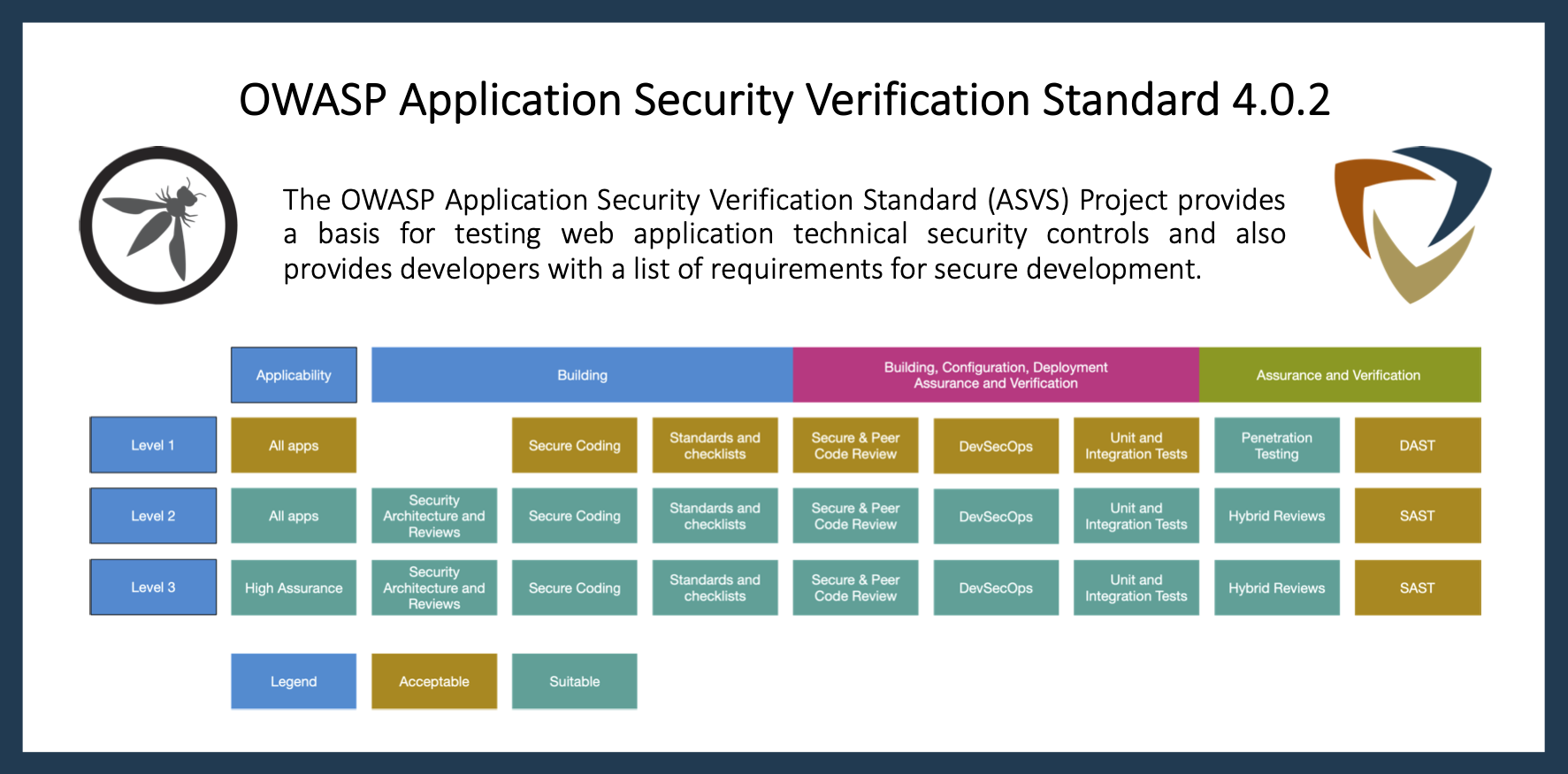
Open Web Application Security Project (OWASP) is a source code analysis tool (Static Application Security Testing (SAST) tools), which are designed to analyze source code or compiled versions of code to help find security flaws.
It has some tools to detect problems during the software development phase, it also provides immediate feedback to the developer on issues they might be introducing into the code during code development.
You can check the tools in the table on their website.
All OWASP materials are available under an approved FLOSS license.
GitHub: https://github.com/OWASP
5- Apache Yetus

Apache Yetus is a collection of libraries and tools that enable the contribution and release process for software projects.
It has a list of components like website source, pre-commit, audience annotations, shell docs, release Doc Maker, yetus-maven-plugin, and more.
Apache Yetus is released under the Apache-2.0 license.
GitHub: https://github.com/JD-Software/JDeSurvey
6- OpenSCAP
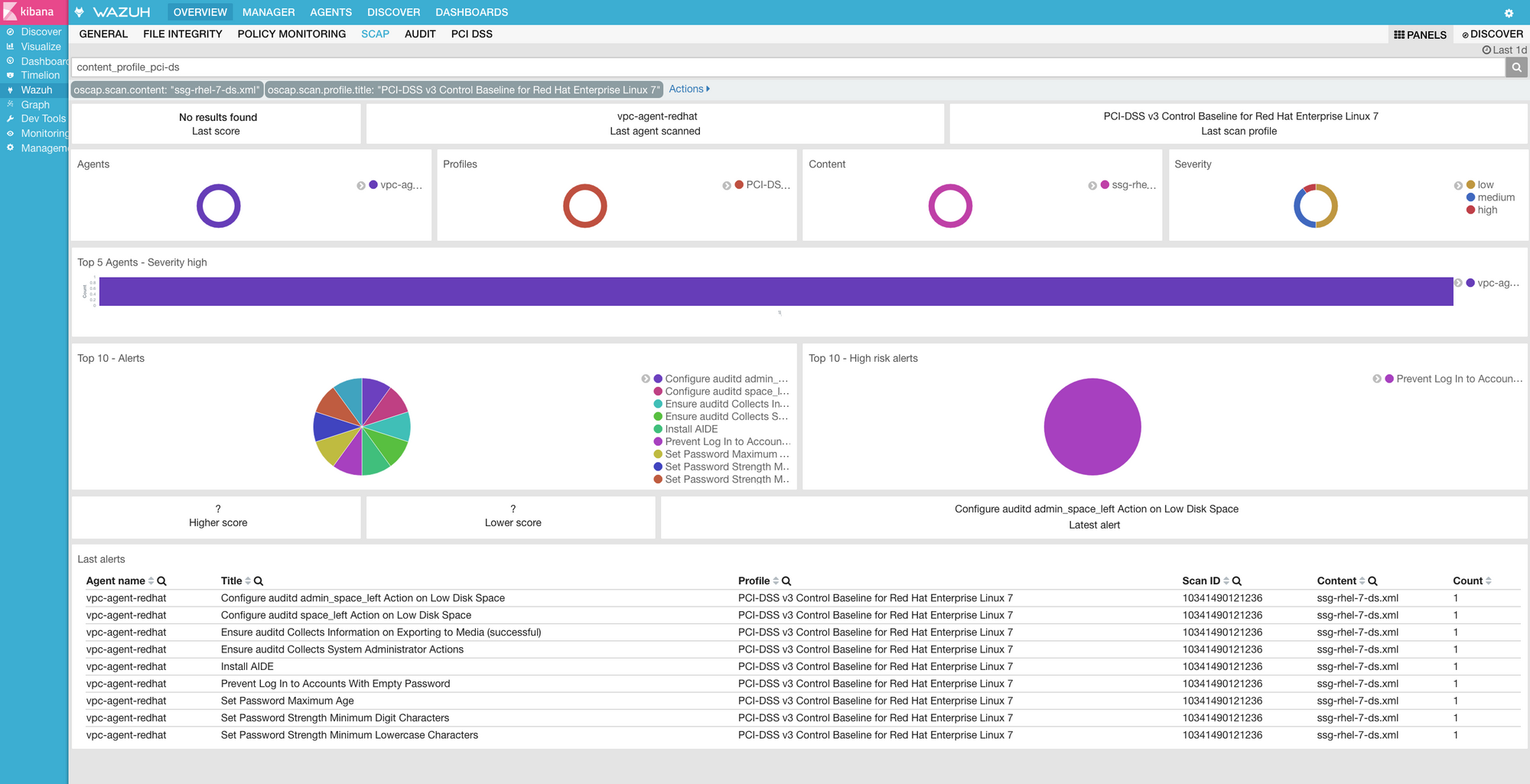
OpenSCAP provides multiple tools to assist administrators and auditors with assessment, measurement, and enforcement of security baselines.
It maintains great flexibility and interoperability, reducing the costs of performing security audits. It aims to perform configuration and vulnerability scans of a local system.
Furthermore, it is free to use on any platform, the source code of all OpenSCAP tools is public, it provides tools and customizable policies for a quick, cost-effective, and flexible implementation, it represents both a library and a command-line tool.
OpenSCAP is available on various Linux distributions, including Red Hat Enterprise Linux, Fedora, and Ubuntu. OpenSCAP currently is working on Microsoft Windows since 1.3.0 its release.
The project is released under the LGPL-2.1 license.
GitHub: https://github.com/OpenSCAP
7- SonarQube
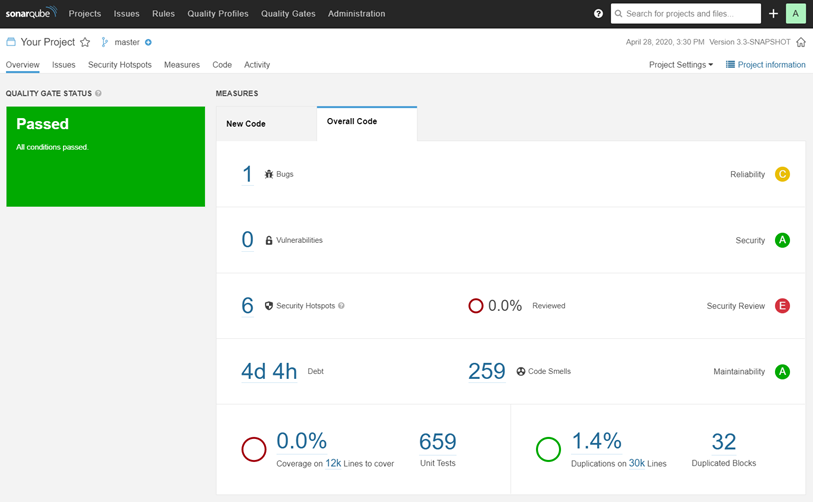
SonarQube is an open-source for developers to write cleaner and safer code.
With it, you can enhance your workflow with continuous code quality and code security, catch tricky bugs to prevent undefined behavior from impacting end-users and fix vulnerabilities that compromise your app. It also will make sure that your codebase is clean and maintainable, to increase developer velocity.
SonarQube wrote with java and was licensed under the LGPL-3.0 license.
GitHub: https://github.com/SonarSource/sonarqube
8- Metasploit
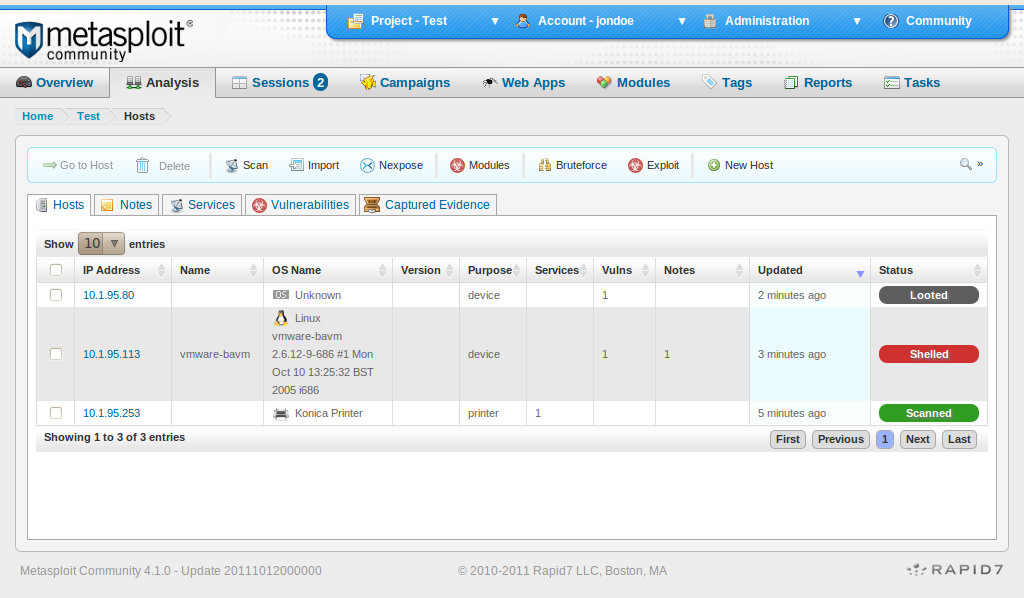
Metasploit is a penetration testing framework for offensive security teams. It was released under a BSD-style license.
It is a vulnerability validation tool that helps you divide the penetration testing workflow into manageable sections.
Furthermore, Metasploit contains a command-line interface, third-party import, manual exploit, action, and manual brute-forcing.
Metasploit free version includes Zenmap, a security scanner, and a compiler for Ruby.
GitHub: https://github.com/rapid7/metasploit-framework
9- Security Knowledge Framework
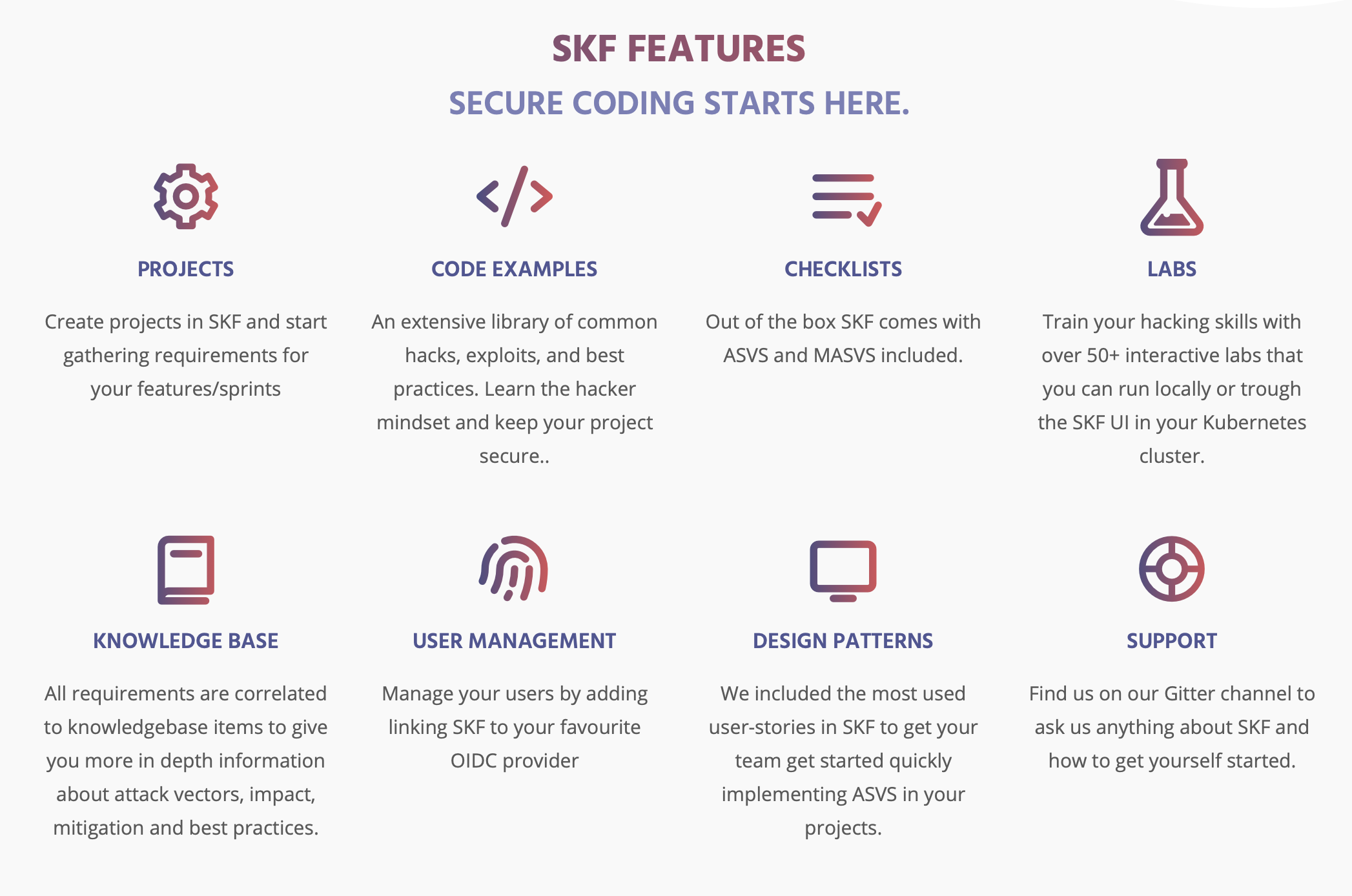
SKF an open-source security knowledge framework that will train you and your team in writing secure code, by design. It is based on a Python-Flask web application that uses the OWASP Application Security Verification Standard.
It helps you to write a secure code with your team. With it, you can create projects and start gathering requirements for your features/sprints, it has many code examples, it comes with ASVS and MASVS, you can train on your hacking skills with over 50+ interactive labs, it is user management.
SKF is a Python Flask / Angular project and is licensed under the GNU 3.0 license.
GitHub: https://github.com/blabla1337/skf-flask
10- FOSSA
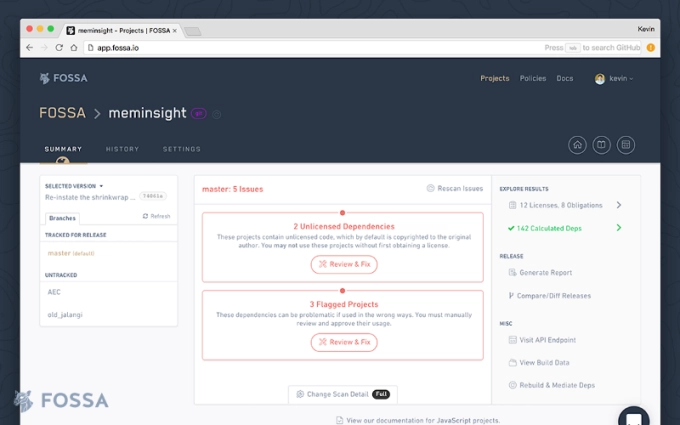
Another good, easy and flexible drive open-source dependency management for enterprise teams. With automated compliance, security, and quality.
FOSSA wants to help developers manage the tricky terrain of open-source license management.
It features universal identification, scalable governance, enterprise-grade reporting, automated, real-time protection from vulnerabilities.
It also supports license and vulnerability scanning for large monoliths. Language-agnostic; integrates with 20+ build systems.
FOSA is built with Go language and licensed under MPL-2.0 license.
GitHub: https://github.com/fossas
If you have any additional software you would like to see in this list, then we would love to hear about them in the comments.


