Reading and Processing Large Files in Python
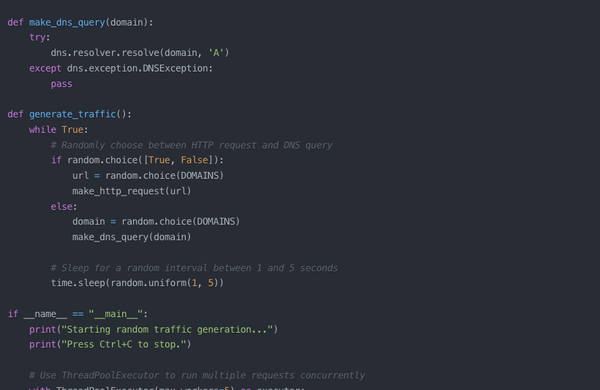
To read a large text file in Python without loading it into memory, you use a technique that reads the file line by line. This is achieved by opening the file in a context manager (with statement) and iterating over it with a for loop.
Each iteration reads a single line into memory, processes it, and then discards it before moving to the next line. This method is highly efficient for large files as it significantly reduces memory consumption.
To read large text, JSON, or CSV files in Python efficiently, you can use various strategies such as reading in chunks, using libraries designed for large files, or leveraging Python's built-in functionalities.
Here are code snippets for each:
1- Reading Large Text file using Python
with open('large_file.txt', 'r') as file:
for line in file:
process(line) # Replace 'process' with your actual processing logic
2- using Pandas to read large CSV files
import pandas as pd
chunk_size = 50000 # Adjust based on your memory constraints
for chunk in pd.read_csv('large_file.csv', chunksize=chunk_size):
process(chunk) # Your processing logic here
3- Using ijson Library to read large JSON files
with open('large_file.txt', 'r') as file:
for line in file:
process(line) # Replace 'process' with your actual processing logic