SpiderFoot: Self-hosted Open-source Intelligence Automation (OSINT) Tool
SpiderFoot automates OSINT for threat intelligence and mapping your attack surface.
Table of Content
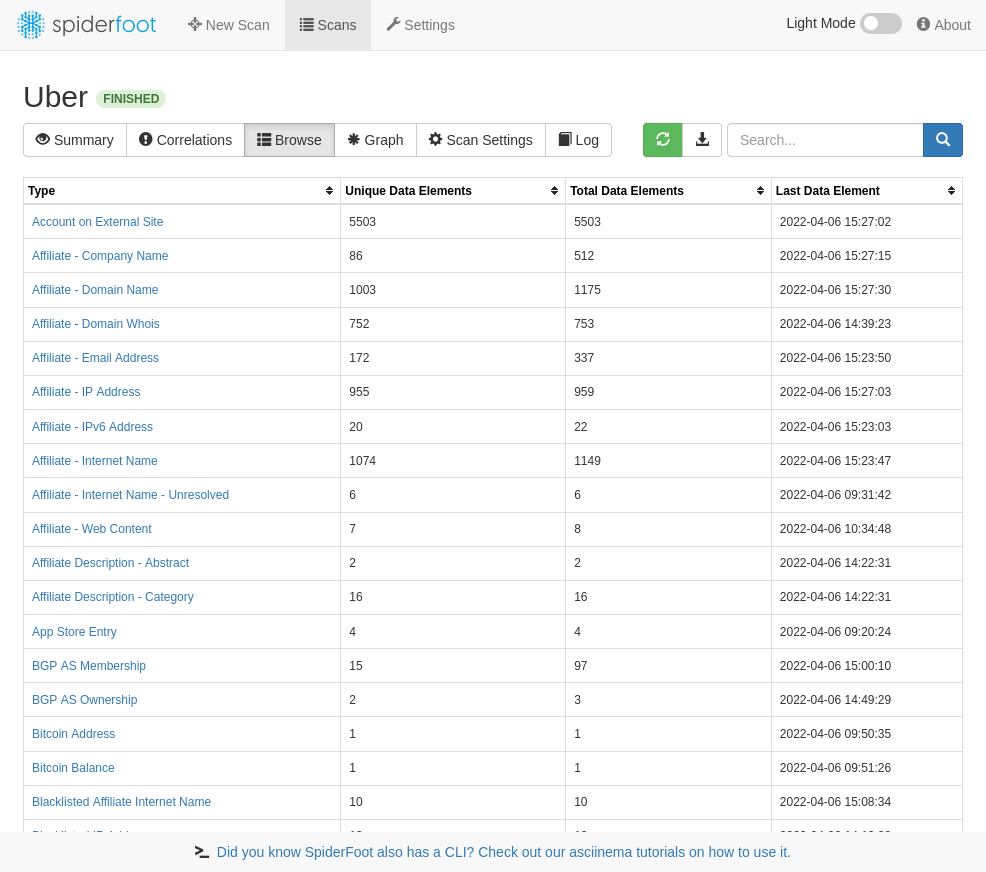
SpiderFoot is an open source intelligence (OSINT) automation tool. It integrates with just about every data source available and utilises a range of methods for data analysis, making that data easy to navigate.
SpiderFoot is a highly useful automated system that can help automate the process of gathering intelligence about a given target, which could be an IP address, domain name, hostname, or network subnet.
This tool can be highly effective in both offensive and defensive contexts. It can be employed in a black-box penetration test to gather information about the target, or used defensively to identify any information that your organization may be freely providing for attackers to use against you.
Using SpiderFoot can significantly enhance the security of your organization by enabling you to gain greater insights into the vulnerabilities of your network, and identify areas where improvements need to be made.
Its powerful features and easy-to-use interface make it a top choice for security professionals who are looking for a comprehensive and reliable tool to help them better manage and protect their networks.
SpiderFoot has an embedded web-server for providing a clean and intuitive web-based interface but can also be used completely via the command-line. It's written in Python 3 and MIT-licensed.
Moreover, SpiderFoot is constantly being updated with new features and functionalities, ensuring that it remains at the cutting-edge of the industry. This means that you can rest assured that your organization is using only the latest and most advanced intelligence automation tool available, helping you stay one step ahead of potential threats.
Features
- Web based UI or CLI
- Over 200 modules (see below)
- Python 3.7+
- YAML-configurable correlation engine with 37 pre-defined rules
- CSV/JSON/GEXF export
- API key export/import
- SQLite back-end for custom querying
- Highly configurable
- Fully documented
- Visualisations
- TOR integration for dark web searching
- Dockerfile for Docker-based deployments
- Can call other tools like DNSTwist, Whatweb, Nmap and CMSeeK
- 100% Cloud-based and managed for you
- Attack Surface Monitoring with change notifications by email, REST and Slack
- Multiple targets per scan
- Multi-user collaboration
- Authenticated and 2FA
- Investigations
- Customer support
- Third party tools pre-installed & configured
- Drive it with a fully RESTful API
- TOR integration built-in
- Screenshotting
- Bring your own Python SpiderFoot modules
- Feed scan data to Splunk, ElasticSearch and REST endpoints
Uses
SpiderFoot can be used offensively (e.g. in a red team exercise or penetration test) for reconnaissance of your target or defensively to gather information about what you or your organisation might have exposed over the Internet.
You can target the following entities in a SpiderFoot scan:
- IP address
- Domain/sub-domain name
- Hostname
- Network subnet (CIDR)
- ASN
- E-mail address
- Phone number
- Username
- Person's name
- Bitcoin address
SpiderFoot's 200+ modules feed each other in a publisher/subscriber model to ensure maximum data extraction to do things like:
- Host/sub-domain/TLD enumeration/extraction
- Email address, phone number and human name extraction
- Bitcoin and Ethereum address extraction
- Check for susceptibility to sub-domain hijacking
- DNS zone transfers
- Threat intelligence and Blacklist queries
- API integration with SHODAN, HaveIBeenPwned, GreyNoise, AlienVault, SecurityTrails, etc.
- Social media account enumeration
- S3/Azure/Digitalocean bucket enumeration/scraping
- IP geo-location
- Web scraping, web content analysis
- Image, document and binary file meta data analysis
- Dark web searches
- Port scanning and banner grabbing
- Data breach searches
License
GNU General Public License version 2.0 (GPLv2)
Resources
- Home
- Sourceforge
- GitHub