Understanding the Risks and Rewards of Open-Source Software in Healthcare
Open-source software (OSS) has become an integral part of the technology landscape, offering numerous benefits but also presenting unique challenges, especially in the healthcare sector.
This post explores the history, advantages, and potential risks associated with OSS, with a particular focus on its application in healthcare.
What is Open-Source Software (OSS)?
Open-source software refers to software whose source code is freely available for anyone to download, modify, and share.
This transparency fosters a collaborative environment where developers worldwide contribute to software improvements. Notable examples of OSS include Firefox and Linux.
A Brief History of Open-Source Software
The roots of OSS trace back to the early days of computing when sharing knowledge freely was the norm among scientists and researchers.
Despite the commercialisation of software development and the dominance of major software firms, the tradition of creating and sharing open-source software has persisted thanks to dedicated hobbyists and communities.
Recent Developments in OSS
Several key events have shaped the current landscape of OSS:
- October 2023: The FDA mandated that all medical devices running software must maintain a software bill of materials (SBOM), including OSS.
- September 2022: The Securing Open Source Software Act of 2022 was introduced to the Senate.
- February 2022: NIST published the Secure Software Development Framework (SSDF) v1.1.
- May 2021: NIST issued guidance on software supply chain security as part of Executive Order 14028.
The Prevalence of OSS
OSS forms the backbone of software across critical infrastructure sectors. A study by Synopsys found that 96% of codebases in various sectors contain OSS, with 76% of the code in these codebases being open-source.
Benefits of Open-Source Software
OSS offers several advantages, including:
- Lower initial costs
- Faster project initiation and iteration
- Flexibility in software development
- Strong community-driven support
- Increased feedback and collaboration
- Simplified license management
The Double-Edged Sword of OSS
Despite its benefits, OSS can also be the weakest link in the software supply chain. Common risks include:
- Known vulnerabilities, due to its open nature, the solution vulnerabilities are exposed to the public sometimes even before finding a solution by the community.
- Compromised legitimate packages
- Name confusion attacks

Concerns with Open-Source Software
Publicly Accessible Code and Vulnerabilities
While public access to code can enhance collaboration, it also allows malicious actors to find and exploit vulnerabilities.
Unpatched vulnerabilities in OSS libraries can propagate through thousands of applications, weakening entire supply chains.
Constant Updates Are Necessary
OSS requires frequent updates to address security vulnerabilities. However, developers often fail to keep OSS components up-to-date, leaving systems vulnerable.
Lack of Testing and Accountability
OSS projects typically lack centralized quality control and dedicated support, making rigorous testing and accountability for security issues challenging.
Open-Source Software in Healthcare
Industry Exposure to OSS
The healthcare sector has seen a significant increase in the use of OSS, with codebases containing OSS growing from around 65% in 2018 to roughly 80% in 2022.
However, the percentage of codebases with high-risk vulnerabilities has fluctuated, rising again recently.
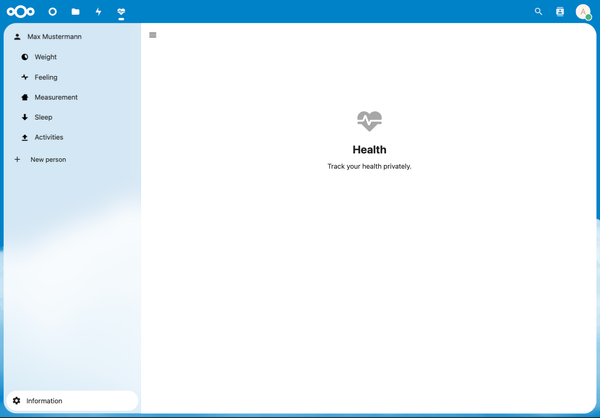
Examples of OSS in Healthcare
- Electronic Medical Records (EMR): OpenEMR, OpenMRS, OpenClinic
- Inventory Management: HospitalRun, MedSupply
- Prescription Software: OPENeP, Open Hospital
- Laboratory Management: OpenLIMS, FreeLIMS
- Clinic Management: OpenClinic, Mr. Tooth
- Medical Billing: OpenEMR, MedManage
Threats to Medical Devices with OSS
While no documented cyberattacks have directly targeted medical devices, ransomware attacks have disrupted systems that include x-ray machines and other devices.
Vulnerabilities in OSS can potentially compromise the functionality of medical devices like insulin pumps and defibrillators.
Case Studies in Healthcare
Prior OSS Vulnerabilities
- August 2014: The Heartbleed flaw in OpenSSL affected two-thirds of websites, including healthcare systems, leading to significant data breaches.
- August 2020: Zero-day vulnerabilities in a hospital's information management system exposed sensitive patient information.
- December 2021: The Log4Shell bug in the Apache Log4j Project allowed attackers to exploit medical devices.
- January 2023: Vulnerabilities in the OpenEMR system exposed sensitive information and compromised entire systems.

Case Studies in Other Industries
OSS Supply Chain Attacks in Banking
The banking sector has also faced OSS supply chain attacks, showcasing the deceptive tactics used by attackers and underscoring the need for robust security measures.
North Korea Weaponizing OSS
The North Korean Lazarus hacking group has used OSS to infiltrate corporate networks across various industries, demonstrating the global nature of OSS threats.
Open-Source Tools Used in Attacks
Malicious open-source tools like SapphireStealer have been used to steal sensitive information, highlighting the need for vigilance in using and managing OSS.
Mitigations for Malicious Package Attacks
To prevent malicious package attacks, best practices include verifying package authenticity, scanning packages for vulnerabilities, inspecting DNS settings, performing code reviews, and verifying package checksums.
Open-Source Security Measures
Open Source Security and SLSA
The Open Source Security Foundation (OpenSSF) has introduced Supply-chain Levels for Software Artifacts (SLSA) to improve OSS security.
Evaluating OSS
Evaluations should scrutinize development methodology, community activity, codebase security, and the maintainers' responsiveness to security issues.
Software Bill of Materials (SBOMs)
SBOMs list all components and dependencies in software, helping identify vulnerabilities and manage security risks.
Software Composition Analysis (SCA)
SCA tools automate the identification of OSS in codebases and generate SBOMs, notifying developers of vulnerabilities as they add packages.
CISA's Open Source Software Security Roadmap
The Cybersecurity and Infrastructure Security Agency (CISA) released a roadmap in September 2023 outlining goals to support OSS security, reduce federal government risks, and harden the OSS ecosystem.
Conclusion
OSS plays a crucial role in modern software development, offering numerous benefits but also presenting significant risks. In the healthcare sector, the use of OSS necessitates robust security measures, including regular updates, thorough evaluations, and comprehensive security frameworks.
By understanding and addressing these challenges, healthcare organizations can harness the power of OSS while mitigating potential threats.